Sterlingov Appeal: The Criminalization of Privacy
The Department of Justice has repeatedly opined that cryptocurrency mixers are legal. That may be true in theory, but doesn't translate into practice, the appellate court in Washington DC appeared to argue today.
Roman Sterlingov was arrested in April 2021 at Los Angeles International Airport and indicted almost a year later, in July 2022, for running the early custodial bitcoin mixer, Bitcoin Fog. According to the government, the mixer processed close to $336 million in bitcoin, including $78 million related to darknet markets like Silk Road, Agora, AlphaBay and Evolution.
In 2024, Sterlingov, a Swedish national, was found guilty of conspiracy to commit money laundering as well as several counts of violations of federal and state money transmission laws, and sentenced to 12.5 years in prison.
Today, the United States Court of Appeals for the District of Columbia Circuit heard the defense and prosecution's arguments in Sterlingov's appeal, which mainly focused on the discussion of venue.
The three judge panel appears to have given the case a thorough read, Sterlingov’s attorney Tor Ekeland told The Rage after the hearing. “It’s a very smart court, I think they’re looking at this intensely, I have no idea what they’re going to do,” he added.

All Mixer Funds – Licit or Illicit – As Part of the Criminal Conspiracy
Opening their argumentation, the defense laid out that a federal agent sending an incriminating email to the Bitcoin Fog service, which was never responded to, and consequently utilizing the service from the District of Columbia, was not enough to establish venue against Sterlingov on the count of conspiracy to commit money laundering, as the federal agent conducting said transaction had no criminal intent, and no communication between the agent and the operator of Bitcoin Fog actually took place.
"In the indictment, there’s no reference to anything happening in DC. There’s no evidence, anywhere in the record, showing any kind of conspiratorial act in the District of Columbia, nor does the gov point to any in its opposition brief," Ekeland argued.
One of the judges appeared to disagree, surfacing the same argumentation that has recently been brought against Tornado Cash developer Roman Storm by the Southern District of New York: "Every payment in[to Bitcoin Fog] is part of advancing the conspiracy because it increases the size of the pool of bitcoin funds that are shuffling around and obscuring identities," the judge stated.
But mixers are legal, the defense reminded the judges. Yes, they responded, but Bitcoin Fog wasn't – because it was used for money laundering.
The overarching line of argumentation seems to be that mixers are legal in theory, but that this legality does not actually translate into practice. Bitcoin Fog's custodial nature aside, the Government has repeatedly held that software developers should not be held liable for the conduct of their users. And since 2014, FinCEN has held that non-custodial services do not fall under Bank Secrecy Act requirements to identify their users.
But, as the judges in Sterlingov's appeal appear to have held today: once a criminal utilizes your service, all inflows can count toward the criminal conspiracy as licit bitcoin are necessary to cover up illicit funds.
"If its whole purpose - and this is the Jury's conviction here – was for money laundering," one of the judges argued today, "maybe not exclusive money laundering, but it was used for money laundering – and bitcoin was coming from many different sources in the mix and it obscured the bitcoin from criminal sources — that seems to me an act essential to the criminal conspiracy."
A similar exception on knowledge of the criminal utilization of a software has recently been made by acting Attorney General Todd Blanche in a panel discussion at the Bitcoin Conference in Las Vegas: "If you are developing software, if you are a coder, if you were part of that process — and you are not the third-party user, and you are not helping and knowing that the third party is using what you develop to commit crimes — you are not going to be investigated and not going to be charged," Blanche told the audience.
A recent draft of the Senate Banking Committee's CLARITY Act now carves out protections for non-custodial developers, in which the knowledge requirement remains but appears tied to specific intent to help a criminal move funds.
"Respond to an email w/ support to launder funds & you are not safe," CoinCenter CEO Peter van Valkenburgh posted on the latest CLARITY draft on X. Or, as in the case of Sterlingov, don't respond at all:
As the prosecution argued today, Sterlingov had spent much of his time online, and much of his focus was dedicated to Bitcoin Fog, therefore the jury could reasonably infer that he had seen the incriminating message sent by the federal agent within the two days of the agent's funds having been received and sent back out by his service.

Who Can the US Prosecute for Unlicensed Money Transmission?
Much of the hearing then focused on whether a federal agent receiving money from an overseas service was enough to justify US jurisdiction, especially around the licensing requirements for money transmission businesses within the US.
"You need some kind of evidence that something occurred. If this is the standard for internet cases than any federal agent from a keyboard can send a message to any website anywhere in the world that doesn’t get a response," Ekeland argued. But he did get a response, one of the judges countered. He received the Bitcoin back – and therefore received a service. But was that enough to establish venue?
"If you make one transaction, even if it is completely lawful, if you haven’t registered with FinCEN, you’re criminally liable? For having done that one transaction? Is that your theory?," one of the judges asked the prosecution, to which the government responded that there was more than one transaction that was made by undercover agents.
"But you're not arguing that it's a two transaction threshold," the judge replied. "Money transmission in the DC code refers to seeding money for transmission or transmitting money within the United States – in other words, the defendant would have to have received money within the US, have to have been in the US when the business received or transmitted money, but the business did neither of these things. It transmitted money from Sweden to the United States."
"If a US business is sending a money transaction to Azerbaijan," the judge continued, "and Azerbaijan said you’re not registered, you have one Million Dollar criminal penalty – really? That’s the position of the United States? That’s totally fine under due process to satisfy the venue clause of the constitution?"
"If you have an international business doing 521,000 deposits and 693,000 withdrawals, and you know, he’s posting in English on Bitcoin Talk," the prosecution countered. "In a post which he made in his own name he refers to the fact that you can use Tor to evade even US law enforcement, indicating that he understands that his service may be especially attractive to people in the United States."
"I suspect that PayPal has registered everywhere in the United States," the prosecution added. "But also everywhere in the world?" the judge countered. "I don't know," the government responded. "But I think that somebody who is running an internet business that is reaching into the United States and is doing business with United States customers, I think they are subjecting themselves to US law and state law."
"Is that right?" the Judge asked. "If I’m running a bank in San Antonio Texas and some of my customers use Zelle to transfer money and some of the customers are in DC, then my San Antonio based bank has to file for a DC money transmission license before I can deal with that Zelle transaction?"
"I don't want to give business advice to businesses in San Antonio," the prosecution replied, stating that she had looked into registration requirements informally, finding it common for financial service businesses to apply for licenses everywhere, and that some businesses find some jurisdictions particularly burdensome that they in fact avoid doing business with customers in that jurisdiction because they don't want to comply with the local laws.
"If [Bitcoin Fog] had any aversion for doing business in the United States, they could have asked the very questions of their customers that legitimate bitcoin businesses do to find out where they’re operating," the prosecution concluded.

Who Operated Bitcoin Fog?
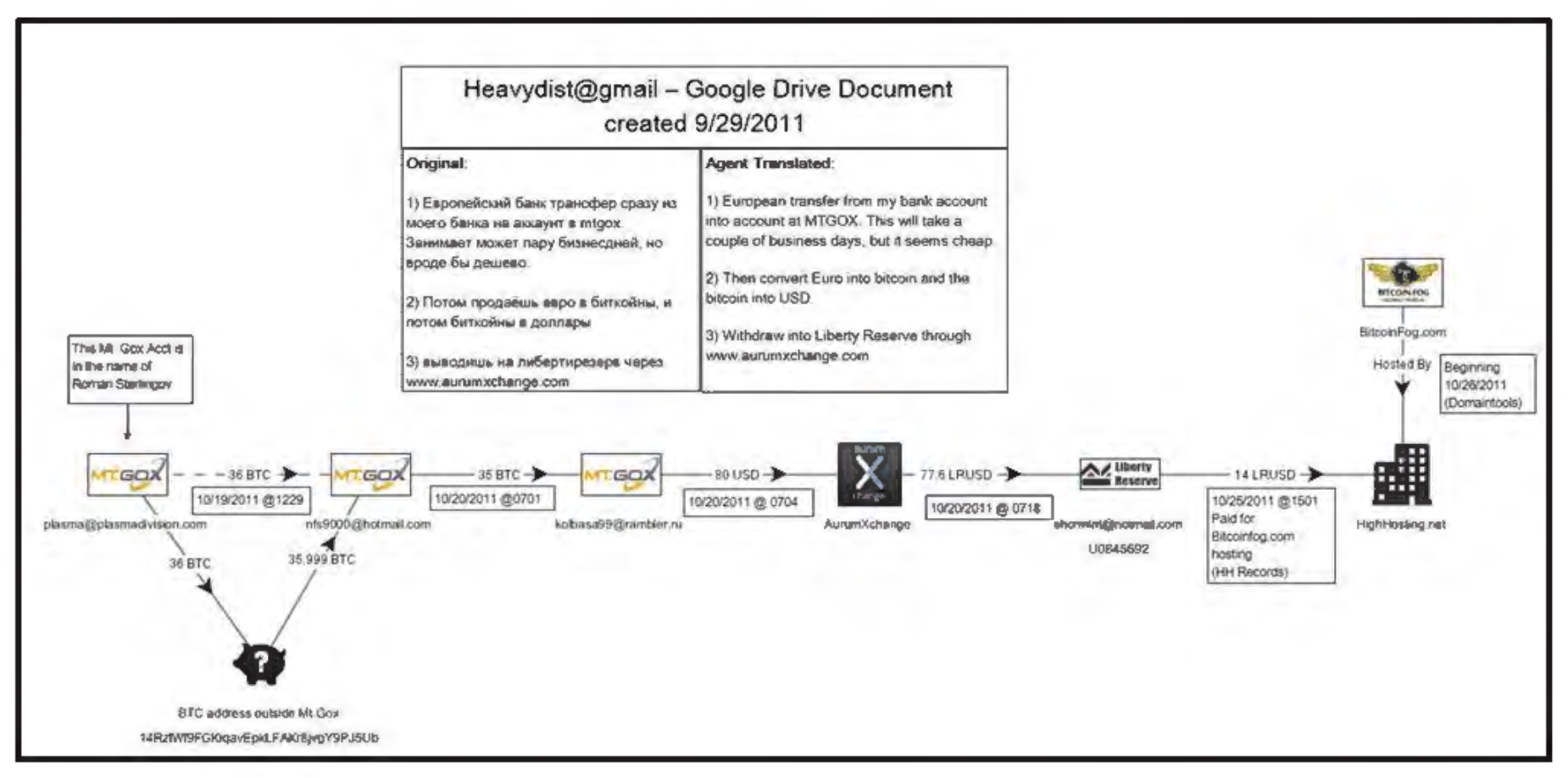
The remaining time of the hearing was spent on how exactly the government identified Sterlingov as Bitcoin Fog's operator. At the heart of the evidence against Sterlingov had lied an IP address which Sterlingov had used to access a Liberty Reserve account registered to his own name – a now defunct currency exchange service. That same IP address was then used to access other accounts at Mt. Gox and Liberty Reserve, which had transacted with the Bitcoin Fog service – But experts have argued that the IP address was likely stemming from a VPN.
"You said that it was 'likely' the same user," one of the judges addressed the prosecution. "What was the reliable basis for that conclusion that it was likely? I didn’t see testimony to that on how rare the number of overlaps is – if they’re still separate but on the same VPN or WiFi or whatever. What was the basis in the record for that?"
The government answered that the basis was that logins to Sterlingov's Liberty Reserve account and Bitcoin Fog affiliated accounts were only a minute apart, and both dealt with cryptocurrency exchanges. Another time, the prosecution added, the IP address was used to sign into Sterlingov's Liberty Reserve account, then into a Bitcoin Fog affiliated exchange account, and back into Sterlingov's personal account, which she described as "sandwiching," making it likely that the acounts were linked to the same person.
"Well likely assumes some sort of baseline of what are the chances that that could happen by chance," the judge stated. "Likely is a comparative term, and usually when you hear this in testimony from an expert there is some baseline as to ordinarily you don't see this kind of overlap, it's one in a thousand times, there's nothing like that here. There's just no framework for a likely conclusion."
"This spells out here's some facts i saw," the judge continued, "and so they must be likely because I saw these facts." That seems to be the type of thing that the Daubert standard – a legal test for the admissibility of expert testimony – was designed to prevent, the judge concluded: "someone coming in saying I saw ABCD and E, and it might be that that's a likely thing without any framework for reference. [...] The whole point of the Daubert gatekeeping function is that we don't let it all in and don't let it all be argued about. There has to be at least some reliable basis for the conclusions," expressing concerns that this was the most substantial evidence introduced to tie Sterlingov's identity to Bitcoin Fog.
The prosecution disagreed, pointing the judge to "layering transactions" made from Sterlingov's own financial accounts to purchase the Bitcoin Fog domain name, which "had nothing to do with the IP address expertise" – except that it did: as the prosecution conceded just seconds later, the jury could infer that on the same day that Sterlingov purchased the domain name, an IP address in Gothenburg, Sweden, where Sterlingov lived – a city of roughly 600,000 people – signed into the "shoremint" Liberty Reserve account associated with Bitcoin Fog. "That's just a fact, that's not opinion testimony," the prosecution stated.
But the actual tracing evidence as presented by government expert witness Luke Scholl has been largely disputed by the defense, showing a Mt. Gox account registered in the name of Roman Sterlingov that transferred 36BTC to a wallet address outside of Mt. Gox, depicted as a large black piggy bank with a question mark.
From there, the funds were traced via multiple hops to Bitcoin Fog, including via the shoremint email address that had been identified via IP address tracing.
Ekeland believes Sterlingov became the focus of the law enforcement because “he was such a boy scout” that back in 2011, he registered with the first bitcoin exchange Mt. Gox under his real name.
“He KYC’ed his account, which wasn’t even required, but his was the only name they could find. What a weird sick lesson of this case is – don’t put your name on anything. Because if you do KYC your stuff, you might get caught up in a government investigation like this. He’s in jail because he followed KYC when he didn’t even have to,” Ekeland told The Rage.
Sterlingov continues to maintain that he was a user of Bitcoin Fog, and not its operator.
Independent journalism does not finance itself. If you enjoyed this article, please consider making a donation. If you would like to note a correction to this article, please email corrections@therage.co